Incredible opportunity
for those with
incredible potential.
Explore Our Curriculum
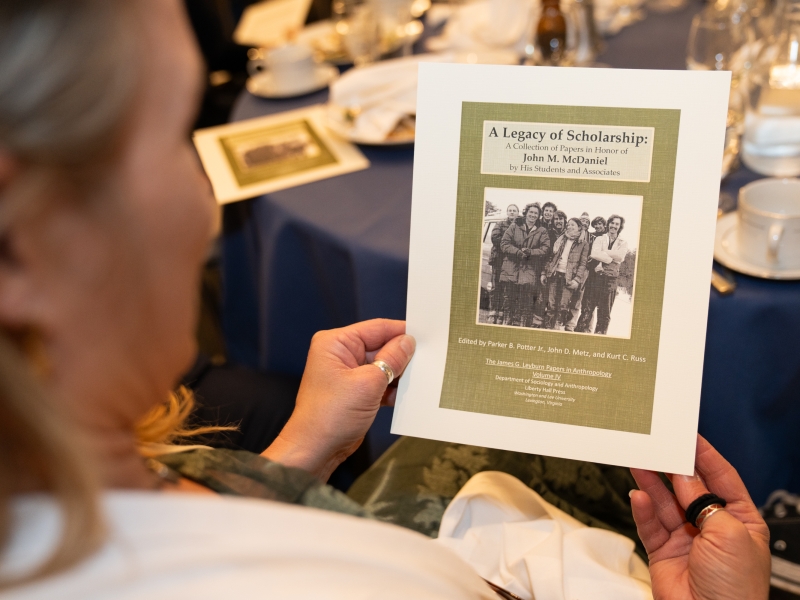
Scene on Campus
Scene on Campus is a frequently updated collection of candid photos highlighting W&L campus life.
Want to see more?
The Heart Of W&L
We have a long tradition of educating smart, ambitious students who have the ability and the desire to make a difference in the world.


Experiential Education
At Washington and Lee University, we believe in the power of learning by doing, so students are encouraged to push beyond traditional classroom experiences.


Global Education
Most students participate in an experience abroad during their W&L experience. This may be for a term or full-year, Spring Term, summer program, internship, research, or service.


Undergraduate Research
Students are encouraged to pursue undergraduate research whether independent or in partnership with faculty.


Distinctively W&L
Our size, resources, innovative teaching and interdisciplinary learning, means students get personal attention and have opportunities for distinctive experiences.
From The Columns
Read The Columns for W&L stories on campus and around the world.